Straight Talk Change Password Wrong Again Change Again
If you're like virtually sophisticated Net aficionados, yous probably have a very articulate thought of what a good password is, and have had to follow the formula to create one over and over again. And, admit it: You probably have just a handful that you lot re-use beyond all the websites you visit.
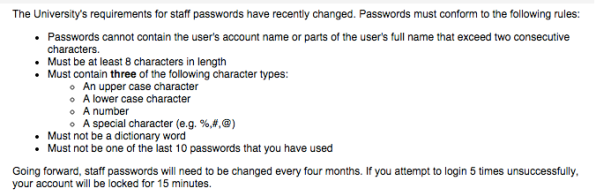
Y'all can recite "good" password rules by heart: viii or more than characters comprising a mix of upper- and lower-case messages, numbers, and punctuation, and omitting the use of any words found in dictionaries, including substitutions (such as @ for a in p@assword or one for lowercase l in fai1).
Yous repeat these rules to less-technical friends and family, and hope they are observing the same kinds of care, although you lot're pretty sure they aren't. Every bit you type a new password (or i of your repertoire) into a website's course field and run across a picayune color bar go from red for a weak password to green for a strong one, you relax a little chip.
You probably also think that you're savvy plenty to avoid being phished: mistaking a imitation site for a existent ane and inbound your credentials into information technology. Yous're attentive to site details, and on sites that offering it, you selection an image that is supposed to jog your memory on your return then you know it's the legitimate site.
"It's a gut feeling when a password has all of these things—uppercase and numbers—how could anyone judge this?" says Markus Jakobsson, an applied security researcher who has written extensively about passwords and studied existent user behavior.
Take a deep breath, because well-nigh of what you've been told about prophylactic passwords is wrong. Observing the rules might result in you creating a password that resists typical cracking techniques. Just y'all could also be devising one that could be croaky in not much more time than "password" or "123456". And even if your password is skilful, the possibility of entering it at a fake site that resembles the one you intended to use is real.
Allow's offset with the basics.
How Passwords Become Cracked
No sensible site stores a countersign as plainly, unencrypted text. For any financial, legal, or medical site, or for sites that process credit cards, it'southward either illegal or against various regulations or terms of service. Rather, they run information technology through a one-way encryption algorithm. The algorithm, known as a "hash," performs a series of operations on the password that transform information technology into an outcome that can't exist reverse engineered.
That is, for whatever given input, the output will be dramatically different and unpredictable. Using the common (but outdated) SHA-1 hashing method, the password 1234 becomes 7110eda4d09e062aa5e4a390b0a572ac0d2c0220, while 1235 becomes ac1ab23d6288711be64a25bf13432baf1e60b2bd. Knowing the output doesn't help yous figure out the original text.
Whenever you log into a site, your countersign—presumably carried over an encrypted https session—is hashed using whatsoever algorithm the site employs, then tested against the version stored in the database.
A cracker who gets ahold of a file of hashed passwords uses creature-force methods to determine what password is associated with which accounts. This starts with using the about normally used passwords, which are easy to observe from previous large-scale attacks and cracks of large databases. It as well includes all words found in dictionaries (English language and others, depending on the site), and and then proceeds to combinations of words.
Shorter passwords using a smaller grapheme fix, such as upper- and lower-case letters, can be cracked exponentially faster than ones that draw from the entire range of characters ane tin type or that are simply longer. Up until a few years ago, crackers congenital "rainbow tables" containing precomputed hashes using popular algorithms equally a way of speeding up cracks confronting the almost frequently chosen passwords. This would seem to bespeak that a complicated and uncommon password like Spooning1! would be a great pick, and that the common wisdom about passwords is accurate. Only not so.
Fauna-force methods using modestly priced computers, which can exist souped up with affordable arrays of graphics cards, tapping into the raw computational power of their graphics processors, can churn through billions to hundreds of billions of passwords per 2d with the SHA-one algorithm. (New algorithms might only allow tens of thousands to hundreds of thousands of checks, but SHA-i remains in wide use for reasons of inertia.)
That amount of computational power ways that crackers now try the likeliest matches in great quantities. Randomly synthetic passwords of 11 or 12 characters that pull from the entire potential character ready remain highly resistant to all just the near determined great. If you utilize a password generator and storage program like 1Password or LastPass to create a unique, random password for each site, you're minimizing your chance enormously.
Just most people don't. And that's where the trouble lies.
To Recall A Countersign, Tell A Story
Markus Jakobsson works at the intersection of security and usability, and his concerns centre around capricious complex password requirements that leave users more exposed to a slap-up attempt, even as a site claims that the password is stiff and resistant.
In an interview, he notes that our minds aren't congenital to think capricious messages, numbers, and punctuation. Rather, we remember stories. When asked to create a password, instead of creating something random, users "have their favorite give-and-take or concept and then just massage it into the correct shape." He says, "We don't tell people strange character sequences, and we're not really wired to remember them."
In his research, he finds someone might try to use the word "apples" because they similar the fruit, simply be told a capital is required. The visitor transforms this into "Apples" only then must add a number and punctuation. They pick the easiest course, and it becomes "Apples1!" This has 8 characters and the requisite variation, and would laissez passer muster at near signup pages. (Some might flag the use of a dictionary word or repeated letters, however.) Dr. Jakobsson says that of these countersign-quality indicators, "They mensurate your likely inability to remember your password."
Crackers bank check dictionary words first with substitutions and common extensions like the above. Based on passwords that are uncovered in early rounds of ciphering, crackers tin can use Markhov chains to predict likely paths to explore, reducing the number of passwords they need to bank check. In mid-2013, Ars Technica consulted with three cracking experts on a leaked database. The experts were able to make up one's mind the passwords in question, with success rates from 60% in ane hour to 90% in 20 hours. While the potential number of fauna-strength password iterations is huge, winnowing and using Markhov chains winnows them downwards.
Dr. Jakobsson has a very dissimilar proposal for a blazon of password he calls "fastwords," which tie together storytelling, password strength, and probability. Reminiscent of a well-known xkcd comic, he suggests coming up with a story that one distills to a few words, such every bit a stepping on a squirrel while running becomes, "running forest squirrel."
Neat of a phrase over x to 12 characters cannot be done finer through creature forcefulness, so crackers would need to effort word combinations and other techniques. Thus the improbability of the combination of three words in that order becomes paramount.
Don't Quote Shakespeare
To decide whether a fastword is as secure every bit possible, information technology'south important to check its likely occurrence in a large corpus of texts. "The fretful porpentine" appears in Shakespeare, and would likely be establish every bit a result in a modest amount of fourth dimension. Jakobsson and a co-author in 1 paper consult Microsoft Research'south petabytes of information in its Spider web N-gram Services, which provides discussion-combination frequency results. The common phrase, "I love y'all honey," occurs at a frequency of 2 in 100,000,000 (2 to the -25.eighth power), making for a very poor password. But a phrase like "frog piece of work apartment"—a story about accidentally squashing a frog on the way to work—is estimated at a rate of 2 to the -49.fifth power or roughly ane in a quintillion odds, a very viable defence against cracking.
The additional advantage of storytelling is resistance to phishing. Many sites employ a mnemonic of having you select an image from a variety of choices or even a word from a list, and ask you to remember that for your next visit. Almost no one does: We don't visit virtually sites often enough to grade an arbitrary association.
In Jakobsson's formulation, an image of the first word in a password could be shown so long as the outset word is sufficiently uncommon; if not, some other word in the password sequence could be shown instead. That word would serve both equally an acknowledgement that you lot were visiting the legitimate site and as a jog to the memory.
For the brusk-term, he hopes for a deviation from an outdated password regimen less likely to help than harm well-nigh users. In the long-term, he believes that a 2d factor—such equally using the fingerprint scanners on phones such as the iPhone 6 and Galaxy S5—will become a strict requirement, rather than an choice that is not always even available. Past adding a second factor, the ability to perform majority countersign bully disappears, even though individuals will remain at varying degrees of vulnerability for someone with a determined reason to crack a unmarried password.
"If they're going to spend 200 hours to interruption into your depository financial institution business relationship and they find you have $500," it'south not worth it, notes Jakobsson. An economic incentive for theft evaporates by making the task so difficult that it's no longer worth the endeavour–which has shut to the same effect as the impossible job of plugging every concluding technical chink in the armor.
Source: https://www.fastcompany.com/3041471/everything-you-know-about-passwords-is-wrong
0 Response to "Straight Talk Change Password Wrong Again Change Again"
Post a Comment